4 of the easiest security gaps to correct for SOC 2 compliance
Achieving SOC 2 compliance begins with a security gap assessment that identifies vulnerabilities, giving you a chance to remediate before it’s too late.
Get the latest insights, information, and news to help you keep up with all that is happening in the fast-moving world of IT!
Achieving SOC 2 compliance begins with a security gap assessment that identifies vulnerabilities, giving you a chance to remediate before it’s too late.
HIPAA compliance is a must for healthcare providers and any third parties they work with. Here’s a HIPAA compliance checklist for IT to help you get started.
HIPAA compliance requirements are intentionally vague, given the rapid pace of technological advancement. Here’s what that means for your business in 2021.
Compliance with DFARS 252.204-7012 demands that organizations adopt sufficient controls to limit the access to sensitive data to authorized users only
Cybersecurity is more a human challenge than a technical one, which is why a strong training program is essential for maintaining compliance
Developing a process for auditing accountability standards throughout the organization is essential for achieving DFARS 252.204-7012 compliance.
The timely maintenance of IT systems is essential for avoiding downtime and keeping risk to a minimum, as well as staying DFARS-compliant
To meet your organization’s DFARS 252.204-7012 obligations, you need to ensure that all risk areas are accounted for
The first thing to do when getting ready for a DFARS 252.204-7012 audit is to evaluate your current security posture with a comprehensive gap assessment.
Traditional perimeter security is no longer enough in the era of distributed computing environments, so here is what you must do to establish boundaries.
Monitoring is easily the most reliable method of tracking accountability and compliance with company policies, and here’s why.
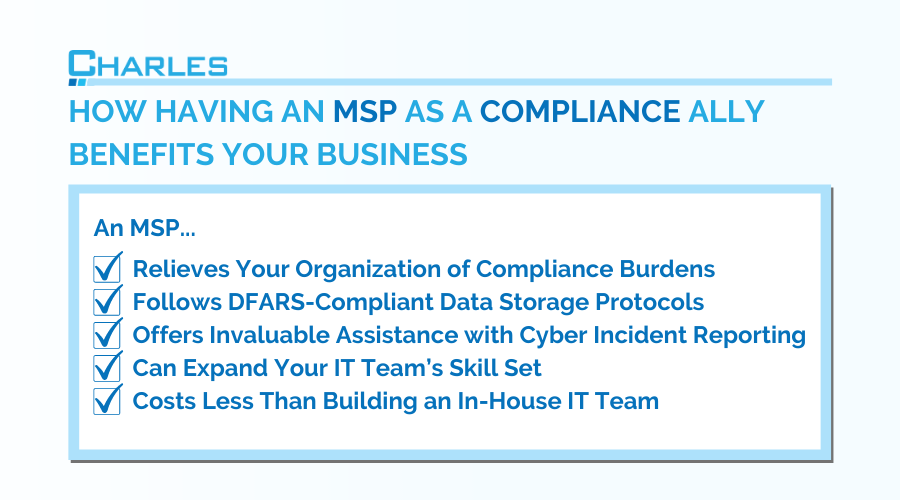
We explore the ways an MSP is your biggest ally in complying with DFARS requirements regarding protecting confidential information and reporting security incidents.
