The rapid development of cyber threats over the years has driven small- and medium-sized businesses (SMBs) in the Northeast and beyond to take a more serious look at their cybersecurity practices. Added to the growing number of cyber threats are the uncertainties that many companies still face regarding policies for remote work and onsite requirements. To simplify, there are more external threats coupled with more internal uncertainty, resulting in greater cyber vulnerability. Just think about it; most homes don’t have the same level of cybersecurity as offices, and cybercriminals can exploit unsecured connections to infiltrate unprotected access points and invade corporate networks.
What Tools to Include in Your Information Technology Planning
If you run an SMB, you should ensure your systems are well-protected against various cyber threats. With the new year less than a month away, here are some of the top cybersecurity services and tools your business should include in your IT budget plan for 2023.
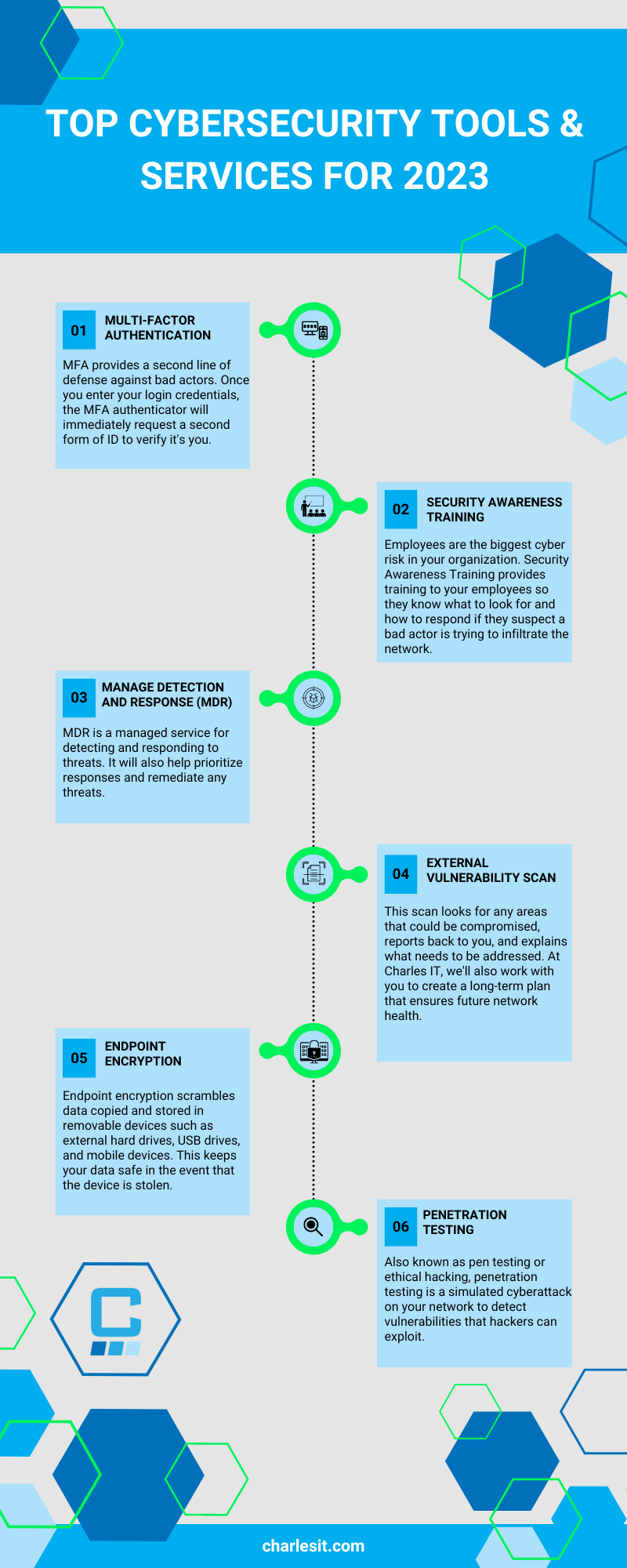
Multi-Factor Authentication (MFA)
On a scale of 1-5, with five being the most confident, how confident are you that your passwords are all strong and unique?
Now, walk around the office and ask that question to your colleagues…don’t worry, we’ll wait.
More likely than not, the average was a three or below.
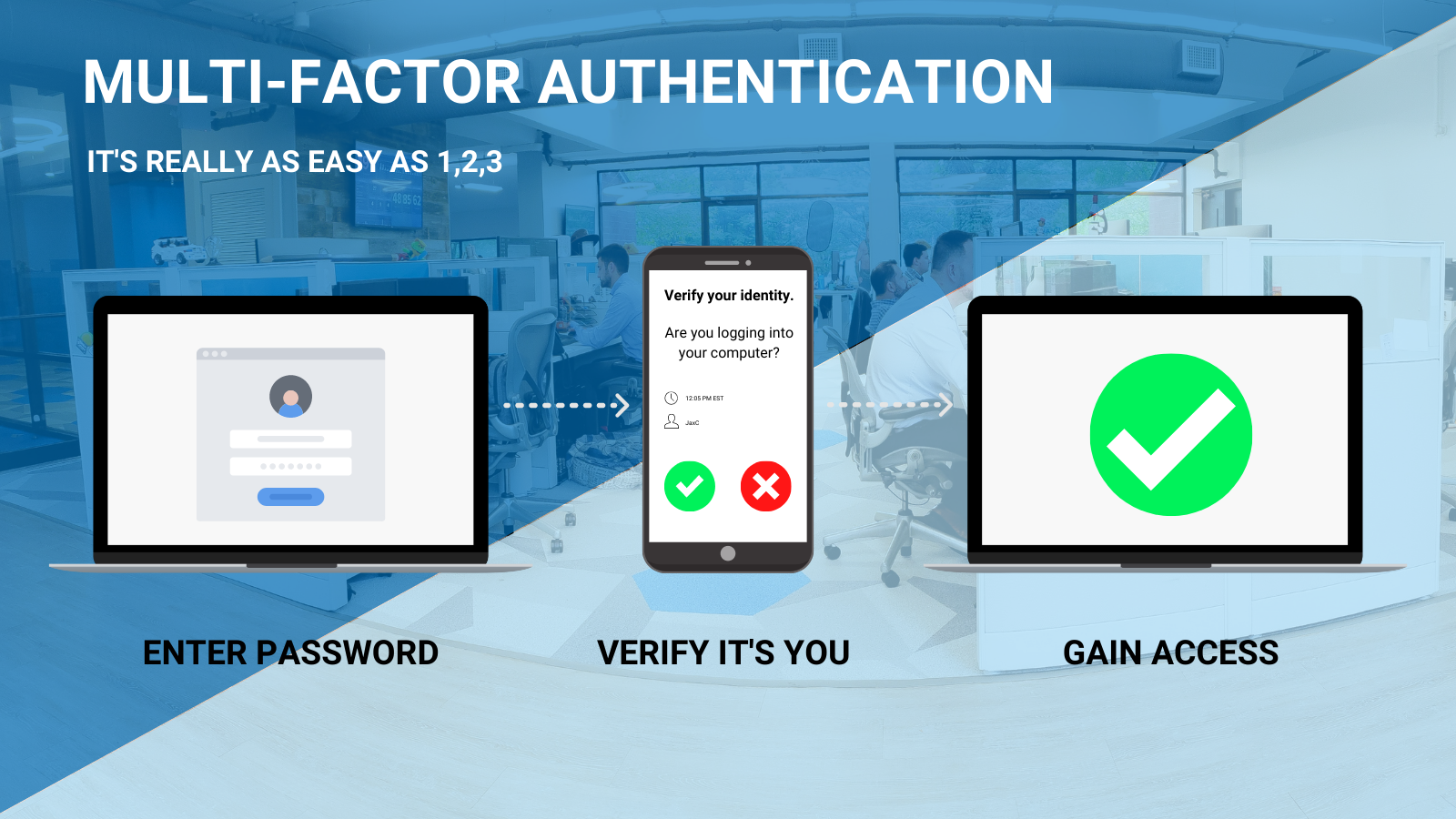
Hackers access your computer network using various methods, like phishing, and often gain access by simply logging in with ill-gotten credentials. While you can log in from anywhere (geographically), multi-factor authentication, or MFA, provides a second line of defense against bad actors. Once you (or someone) enters login credentials, the MFA authenticator that you’re using will immediately request a second form of ID to verify if you are really you.
This “second form of ID” might come in the form of a push notification, text message, secondary code entry, or biometric scanners.
If you’re logging in and it’s business as usual, the process will be simple. However, if a hacker is trying to log in using your credentials, they’ll not only be stopped from gaining access, but you’ll also be notified that someone is attempting to log in using your username and password. MFA allows you to stop the hacker and be aware of all bad actors using your credentials.
| At Charles IT, we use the DUO cloud-based authenticator app and will require MFA for all our clients starting in 2023. |
Security Awareness Training
According to a study by Stanford University, approximately 88% of all data breaches are caused by an employee mistake.
Security Awareness Training provides training to your employees so they know what to look for and how to respond. However, being aware of the risks and possible tactics hackers will use to gain access to your system is only one step in addressing the issue. The other step is ongoing.
In school, you learn about something in the classroom and then are tested on it to ensure comprehension. Cyber security awareness training acts in much the same way.
- Employees are entered into a training program.
- Periodically, employees are sent fake phishing emails and other attempts to [fake] hack their system. (This is the testing part.)
- If the employee “fails” the test by clicking on a bad link, the employee is notified immediately.
- If the employee fails multiple “tests,” they are re-enrolled in the training program (either at full length or an abbreviated version)
Depending on how you structure your security awareness training program, you’ll be able to determine the length of training, difficulty level and frequency of “test” emails, and the re-enrollment training time.
“We need employees to be far more aware of things that they wouldn’t need to be aware of when they’re working in the office,” says Nadya Bartol, Managing Director, BCG. (Forbes.com)
| Charles IT uses the KnowBe4 security awareness training program for all new hires and recommends it to all our clients. In 2022, KnowBe4 received the highest score in a Forrester Research study on Security Awareness and Training Solutions. |
Managed Detection and Response (MDR)
In a nutshell, MDR is a managed service for detecting and responding to threats.
Unless you have a substantial IT department and dedicated resources to hunt down cyber threats in your network, we recommend outsourcing to a managed service provider (MSP). Once the MDR solution detects an intrusion, malicious activity, or malware, it will help an analyst (yes, there’s a human component here) prioritize alerts based on risk levels, respond to each incident, and remediate any threats.
We like to refer to MDR as your very own 24-hour surveillance team.
External Vulnerability Scanning
These are programs designed to identify vulnerabilities in web applications by analyzing each file within the website. It conducts an automatic security audit and looks for loopholes in proxy servers, web servers, web application servers, and other web services that hackers can exploit to gain access to your network, obtain your data and sell it on the dark web.
Simply put, it looks for any areas that could be compromised, reports back to you, and explains what needs to be addressed. However, we also want to make sure you’re able to make the necessary adjustments so when we do external vulnerability scans with clients, we also work together and create a long-term plan to ensure future network health.
Endpoint Encryption
Endpoint encryption scrambles data copied and stored in removable devices such as external hard drives, USB drives, and mobile devices. The files are encrypted sector by sector and can only be accessed with the correct decryption key. This keeps your data safe in case devices are stolen or lost.
Penetration Testing Tools
Also known as pen testing or ethical hacking, penetration testing is a simulated cyberattack on your network to detect vulnerabilities that hackers can exploit. This can be done either manually or automatically using specialized software applications. You’ll want to invest in pen testing tools that can gather as much information about the target, identify all possible entry points, and discover weak exploitable assets.
Aside from identifying potential weaknesses in your network, penetration testing also checks your company’s cybersecurity policies, compliance requirements, security awareness of your staff, and how quickly they can detect and respond to cyberattacks. This will help your IT team or MSP develop a plan to improve your company’s cybersecurity defenses.
Cyberthreats will continue to evolve, but including the right security tools and services in your IT budget plan will protect your company’s data and prevent costly data breaches.
Another way you can keep your business safe from cyber threats is by partnering with a reliable MSP like Charles IT. We help provide managed IT Services for businesses in the Northeast with all their IT concerns, including network support, cloud hosting, and cybersecurity.
{{cta(‘a0a30d4f-8319-42cf-a537-a868f81b2b1c’)}}