How to Transition From Working From the Office to Working From Home
Ways to make the transition from in office to at home easier due to the COVID-19 outbreak
Get the latest insights, information, and news to help you keep up with all that is happening in the fast-moving world of IT!
Ways to make the transition from in office to at home easier due to the COVID-19 outbreak
Talent spotlight on Charles IT employee Wayne Curtiss
Endpoint encryption is important in meeting the CMMC requirements. Find out what endpoint encryption is and how it helps businesses mitigate risks.
How encryption keeps information safe from data breaches and helps maintain compliance with the DoD CMMC framework.
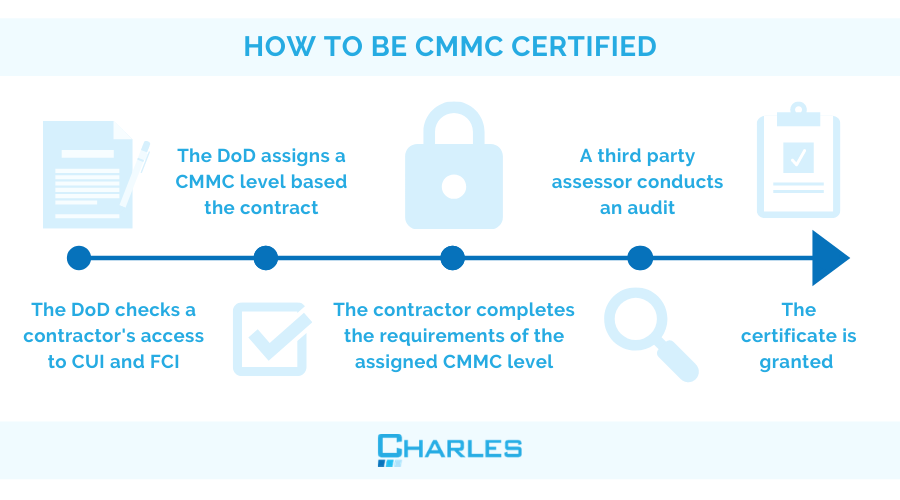
Learn about the 5 CMMC levels and what is the right CMMC certification level for your company
IT budgeting can either be a painful annual process or the actualization of a carefully crafted IT strategy. Use this guide to ensure you avoid the common pitfalls of IT budget planning.

HIPAA regulations went through some major revisions in the past few years. Here is a quick review of those changes.
Configuration management is essential to navigating constant operational changes without adding undue risk to the organization
How deploying the right identification and authentication protocols helps protect controlled unclassified information in accordance with DFARS 252.204-7012
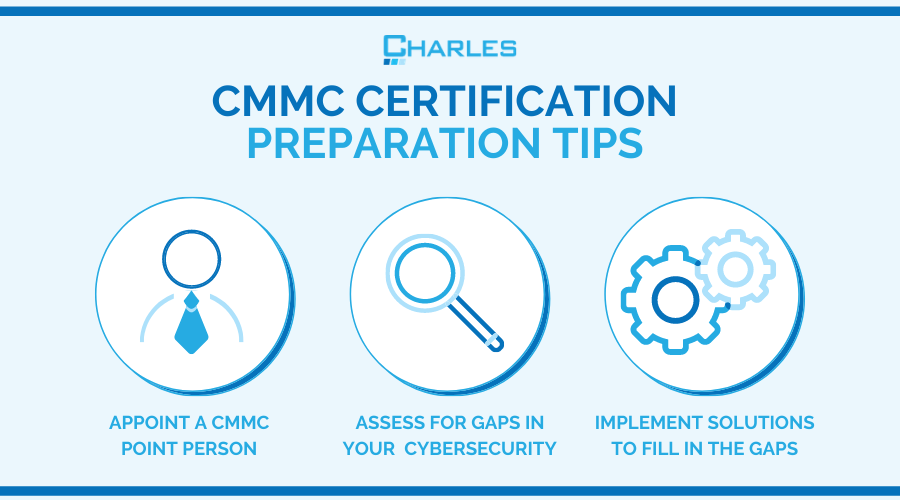
A comprehensive overview of CMMC 1.0, from implementation timeline to differences with DFARS.
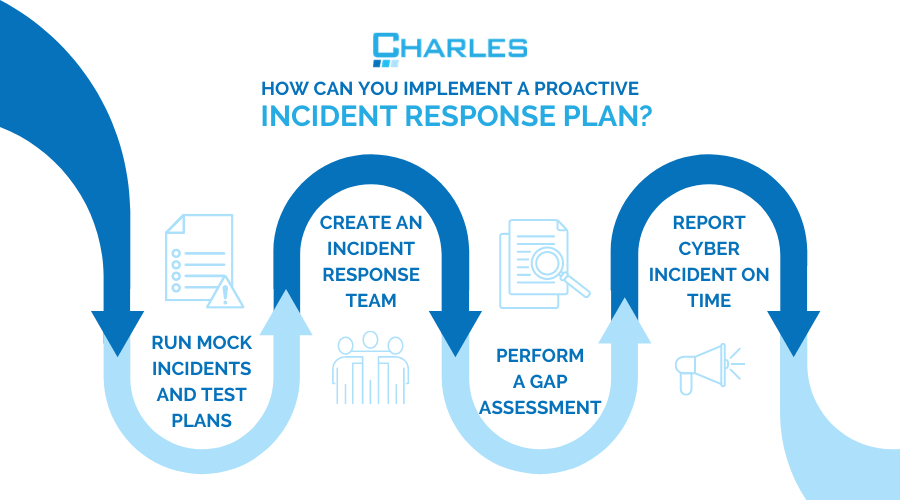
Defense contractors need to have a proactive incident response plan when reporting cyber incidents to ensure compliance with DFARS.
Protecting controlled unclassified information requires paying attention to its entire lifecycle from collection to destruction to comply with DFARS 7012
