IT Budgeting Best Practices: Include A Vulnerability Scanning Program
Vulnerability scanning is a proactive approach to cybersecurity designed to identify and mitigate risks before they become a problem.
Get the latest insights, information, and news to help you keep up with all that is happening in the fast-moving world of IT!
Vulnerability scanning is a proactive approach to cybersecurity designed to identify and mitigate risks before they become a problem.
Every information technology budget sample should account for security and innovation as a single cohesive whole. Here’s how managed services can help.

Incidences of data breaches spike during the holiday season. These cybersecurity tips will ensure your business is protected.

Managed services providers, IT consultants, and other channel partners will become increasingly valuable in the year ahead, and here’s why.
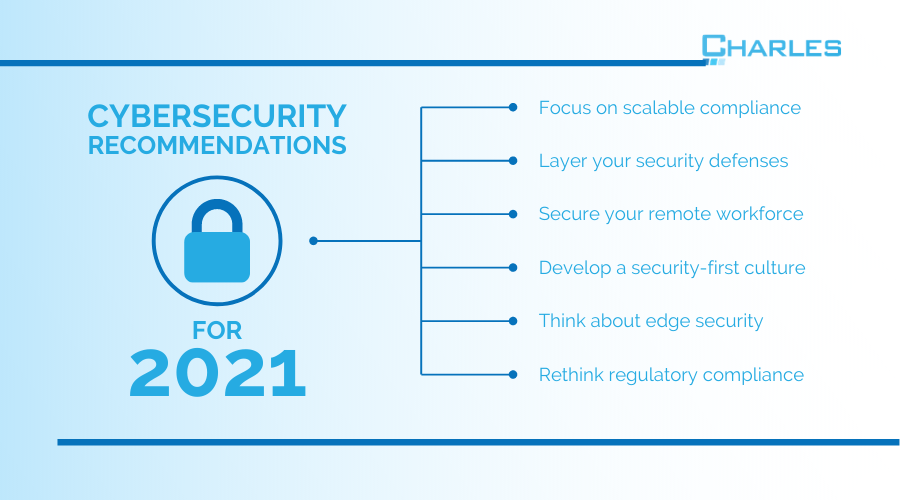
The unprecedented events of 2020 have forced thousands of businesses to rethink the way they approach cybersecurity. Here’s what we recommend for 2021.
With the managed IT services sector evolving rapidly, there are several common misconceptions that businesses need to know about.

Security awareness training is a great way to enhance your company’s cybersecurity posture, defend against cyberthreats, and maintain cyber insurance.

Connecticut’s IT experts explain how data protection starts with people, making cybersecurity awareness training essential for passing your SOC 2 audit.

Connecticut IT Consultants, Charles IT, explain how vulnerability testing can pave the way for your SOC 2 compliance success.
The information security and compliance landscape can be hard for small businesses to navigate, but partnering with the right MSP can make all the difference.

Cybersecurity resilience is crucial for Connecticut manufacturing companies to combat evolving threats and ensure continuous operations.

Effective IT inventory management is crucial for Connecticut businesses. Learn how to optimize IT resources, track assets, and stay compliant with Charles IT’s comprehensive guide.
