Boosting Your Cyber Defenses: The Importance of Multi-Factor Authentication
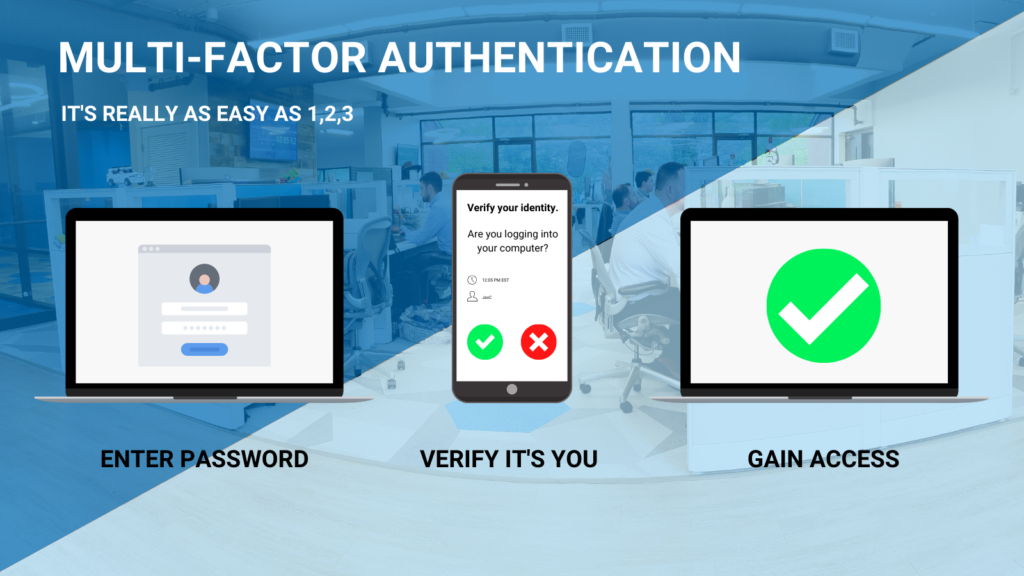
Boost your cyber defenses with Multi-Factor Authentication. Learn how MFA enhances security, mitigates risks, and ensures compliance. Partner with Charles IT for expert MFA implementation. Contact us today.
Mistakes to Avoid When Looking for a CMMC Auditor
Ensure a smooth CMMC audit process by avoiding common mistakes. Learn key pitfalls to steer clear of when searching for a CMMC auditor. Explore our guide for expert advice and insights.
5 Ways an MSP Can Walk You Through Your SOC 2 Audit Process
Navigate your SOC 2 audit process with ease using an MSP. Explore five ways an experienced Managed Service Provider can guide you through the complexities of SOC 2 compliance. Learn more in our comprehensive guide.
5 ways to evaluate HIPAA-compliant storage services
Unlock the key factors for assessing HIPAA-compliant storage solutions with our guide. Learn five essential ways to ensure data security and compliance for your organization. Dive deeper into our blog for expert insights.
Cybersecurity in Manufacturing: Safeguarding Digital Assets

Learn about cybersecurity in manufacturing, safeguarding digital assets with Charles IT’s tailored cybersecurity solutions. Protect against cyber threats, reduce downtime, and ensure compliance.
Acquisition Advantage: MSPs Simplifying Compliance for Expanding SMBs

Discover why Charles IT is a leading MSP for Businesses in Connecticut and New York. We help clients navigate complex regulations with years of expertise!
Unraveling the Mystery of Managed IT: What Every Business Should Know

Unravel the mystery of Managed IT with Charles IT’s solutions for business in Connecticut & New York. Proactive monitoring & strategic planning. Call today!
Building a Cyber-Aware Culture: A Crucial Element for Financial Security

Empower your financial institution with a cyber aware culture & navigate evolving cyber threats. Charles IT is a leading finance IT agency servicing CT & NY
Prevent Costly Penalties: Essential Security Solutions for Compliance and Protection

Discover essential security solutions crucial for businesses to evade punitive damages amid data breaches. Safeguard your organization with effective measures to mitigate risks and ensure compliance.
Navigating SOC 2 Requirements: Avoiding 5 Common Mistakes for Compliance Success

Striving for SOC 2 compliance? Learn the common mistakes to avoid for a smoother journey. Stay on track with SOC 2 requirements and ensure a successful path to compliance.

