NIST Cybersecurity Framework: A Comprehensive Guide

Organizations of all types and sizes face unrelenting threats from malicious actors, including organized cybercrime, corporate espionage, and state-sponsored attackers. Supply chain attacks are on the increase, and supply chains have become an ungovernable size without proper strategy.
The NIST Cybersecurity Framework, or NIST CSF, is a set of recommendations that combine industry standards and best practices to help guide organizations on how to manage risk.
It’s the most widely adopted framework in the United States. It is even the basis of many regulatory regimes, such as the Cybersecurity Maturity Model Certification in the U.S. defense sector.
Every business owes it to themselves, their stakeholders, and their customers to take a proactive stance on IT security and risk management, which is why the NIST Cybersecurity Framework has been adopted globally as the gold standard for information security. Read on to discover how adopting the NIST Cybersecurity Framework can bolster your cybersecurity efforts and open new business opportunities.

Overview of NIST
What is NIST?
Widely viewed as the global standard for best practices in the sector, the NIST Cybersecurity Framework (NIST CSF) guides mitigating information security risks. Consistently revised to address the most pressing challenges, it remains relevant to today’s business leaders and cybersecurity teams.
As the basis for many government- and industry-mandated compliance organizations, the NIST CSF is a thorough and exceptional tool to guard against security threats. The framework is maintained by the National Institute of Standards and Technology, a U.S.-based government organization that seeks to promote innovation without adding unnecessary risk. Though originally developed with U.S. organizations in mind, it serves as a point of reference for many other frameworks and regulatory regimes around the world.
History of the NIST Cybersecurity Framework
The first version of the framework, specifically targeted at the critical infrastructure sector, was published in 2014. This initial release aimed to guide how to enhance cybersecurity across vital industries. In 2017, a draft of a revised version was made available, during which public comments were solicited to ensure the updated framework would meet the evolving needs of the sector.
After considering this feedback, the finalized version was released in 2018. This iteration introduced significant enhancements, including additional details on supply chain risk management and comprehensive guidance on collaborating with external stakeholders to address and disclose vulnerabilities effectively.
The framework itself is also now centered on six core functions of information security, instead of the previous five, to now include the Govern function, which we will address in greater detail in Chapter Three:
This function involves taking inventory of assets that need to be protected, such as servers, virtual machines, endpoints, and networking components. It also focuses on data classification, risk management, and asset vulnerabilities.
This function outlines how well appropriate information security safeguards align with business priorities and environments and information classification levels. Examples of common safeguards include multifactor authentication and endpoint encryption.
Because conventional protective measures are not enough in an era of increasingly sophisticated attacks, this function explores how organizations provide the means to proactively detect potential threats. This may include intrusion detection systems (IDS) and managed detection and response (MDR).
Key roles must be assigned and actions identified should security become compromised. This function centers around what happens when a potential security incident is detected and ensuring that organizations have a documented set of procedures for management.
This function deals with the mitigation strategies needed to restore affected capabilities and services with minimal damage to the organization when security incidents result in unscheduled downtime.
This function addresses the importance of cybersecurity governance. It covers organizational context, risk management strategy, supply chain risk management, and other aspects, to ensure a comprehensive understanding of an organization’s cybersecurity posture.
Today the framework serves as the basis for cybersecurity programs in many industries, especially those in more regulated sectors such as finance, healthcare, and defense.
The NIST CSF can also serve as a basis for achieving compliance with global information privacy regulations, such as CCPA and GDPR. In the healthcare sector, HITECH legislation requires adoption of NIST and other widely recognized cybersecurity standards.
The reality is that many types of businesses, of any size, can benefit from adopting the practices outlined in the framework.
How the NIST Cybersecurity Framework Helps Small Businesses
The mistake that many small businesses make is not considering themselves reasonable targets for more advanced attacks, such as advanced persistent threats (APTs). Because of this misperception, they often have only minimal cybersecurity controls in place to protect against everyday threats such as mass phishing scams and common forms of malware.
The truth is that every organization, no matter the size, is a potential target. In fact, small businesses present something of a sweet spot for attackers, who usually view them as easy targets that nonetheless have a lot of data worth stealing. Even small businesses need enterprise-grade security.
Small businesses that achieve full compliance with the NIST Cybersecurity Framework and the NIST Privacy Framework, make themselves more attractive to potential customers, investors, and suppliers. While achieving compliance might seem like a significant investment, it opens the door to many new business opportunities while greatly reducing the risk facing the organization. Additionally, most cyber insurance providers require NIST compliance to insure any business, making it a crucial step for comprehensive risk management. In sum, it’s a good move for the business’s financial health and reputation.
The NIST Cybersecurity Framework details the various processes and technical measures that need to be applied to detect, respond to, and recover from security-related incidents.
Importantly, achieving NIST small business compliance with the help of the right partners can help to attain the same level of security maturity as large enterprises. For example, a fully managed detection and response (MDR) service can proactively detect and respond to potential threats before they make it past the business’s last line of defenses. Another powerful solution is Security Incident and Event Management (SIEM), which provides in-depth forensic analysis and a complete audit of security-related events across the entire technology environment. Like MDR, this service can also be outsourced and managed externally.
Five Useful Resources for Small Businesses
Full compliance with the framework can be complicated, time-consuming, and costly. Fortunately, NIST provides various helpful resources to help make the process a little less difficult. Let’s review them here.
Official Publications
Start with the institute’s official publications, including of course the NIST Cybersecurity Framework documentation itself. In addition to the official framework, there are over a thousand other publications on the topic of cybersecurity aimed at different technology environments and industries.
Information Technology Laboratory
The Information Technology Laboratory is the best resource center for specific guidelines on all key areas of cybersecurity. The library resources are conveniently divided into three main series. For example, the 500 series details cybersecurity controls and standards all businesses should adhere to, such as multifactor authentication and cloud computing safety. The 800 series provides resources to help businesses align with U.S. government information security standards. Finally, the 1800 series provides operational resources, including guidance on creating your own internal cybersecurity policies and standards.
Cybersecurity Priority Areas
NIST currently lists five priority areas: cybersecurity, the internet of things, artificial intelligence, reliable computing, and future computing technologies. Of these, only the first three are currently available, with the remaining two coming soon. These priority areas are intended to encourage innovation without adding risk.
Computer Security Resource Center
The Computer Security Resource Center is a one-stop shop for everything related to IT security. It is regularly updated to reflect current threats and trends, such as ransomware and operational technology vulnerabilities. In addition to news and updates, you’ll find numerous publications, projects impacting information security, and a list of events you can participate in.
Small Business Center
The Small Business Center provides a variety of useful materials that take into consideration the unique challenges and limitations of small businesses. There is a complete introduction to cybersecurity intended for novices, and extensive planning guides to help you assess your current security measures, training materials, and guidance by topic area.
Summary
By reviewing these resources, business owners and IT professionals can gain insights into the latest cybersecurity standards, guidelines, and recommendations established NIST.
Business owners can benefit from the introduction to cybersecurity and the planning guides, which help them assess their current security measures and identify areas for improvement. IT managers can leverage the specific guidelines and standards outlined in the NIST publications and the Information Technology Laboratory to achieve compliance and enhance the security of their organizations. They can also stay informed about the latest threats and trends through the Computer Security Resource Center, enabling them to proactively address potential vulnerabilities and protect their organizations from cyberattacks.
MSPs, like Charles IT, can help organizations better understand and utilize the resources available to them, by providing guidance, support, and tailored solutions to meet their cybersecurity needs.

Why Following NIST CSF Is Important
The NIST Cybersecurity Framework is the product of many years of research and contributions from numerous leading authorities in the information security sector. As such, it encapsulates the wisdom and experience of the crowd, which is especially important now that technology is everywhere and the threat against it has become increasingly complex as well. This means the framework addresses common oversights and helps business leaders to understand all perspectives on security.
In addition to these obvious benefits of bolstering your cybersecurity plan, here are some other reasons that you may not have considered:

1. Attract High-Value Customers
Information security is much more than a necessity or a costly obligation. Attaining a high degree of security is now a major part of the value proposition. This is especially true for sectors such as defense, healthcare, finance, and legal, in which a brand’s reputation depends heavily on the organization’s ability to protect its clients’ sensitive data. With improved cybersecurity comes a positive ripple effect across supply chains. This makes your organization more attractive to potential suppliers, customers, and investors.
2. Achieve Security Alignment
No longer is there a disconnect between the demands of cybersecurity and broader business goals and priorities. More experts now realize the truth: cybersecurity is everyone’s responsibility, and business success depends on it. The NIST Cybersecurity Framework addresses the needs of risk management and alignment with business needs. Since corporate executives understand this very well, security budgets can be better justified and allocated accordingly.
3. Obtain Cyber Insurance
While strong security measures can mitigate risks, no system is entirely foolproof. Cyber insurance offers financial protection against losses from cyber incidents like attacks or data breaches. These policies cover various expenses such as legal fees, investigations, notification costs, and even ransom payments for ransomware attacks. Having cyber insurance helps businesses recover faster and reduces the financial impact, as well as ensures business continuity. Investing in cyber insurance also enhances the reputation of an organization because it demonstrates a proactive approach to cybersecurity.
NIST CSF Requirements Evolve with The Times
Just as your business adapts to changing external factors, so does the NIST Cybersecurity Framework. For instance, the increase in supply chain attacks in recent years, beginning during the coronavirus pandemic, means that organizations must pay closer attention to vulnerabilities to their vendors, partners, and other external stakeholders. It’s becoming clear that more attacks are originating from third-party organizations. The latest NIST 2.0 framework now includes expansion to the scope and integration of the framework to encompass a global audience. It also has enhanced guidance and governance functions to give organizations practical direction on achieving the subcategories. Additionally, NIST 2.0. adds a new focus on continuous feedback for improvement and a more structured approach to cybersecurity risk management.
The earlier version of the NIST Cybersecurity Framework had been updated to include new guidance on working with supply chain partners and improving vulnerability disclosure processes. With version 1.1, additional measures were added to tackle supply chain risks while also addressing the main challenges faced by business leaders. Now covering a total of six control areas – governance, identification, protection, detection, response, and recovery – the framework offers a set of best practices to guide you through managing the entire lifecycle of cyber threats or incidents. What makes the framework versatile is that the level of detail in security assessments can be interpreted based on individual needs and circumstances. NIST does not prescribe control requirements; Instead, it focuses on high-level requisites.
Using the NIST CSF Tiers as a Gauge
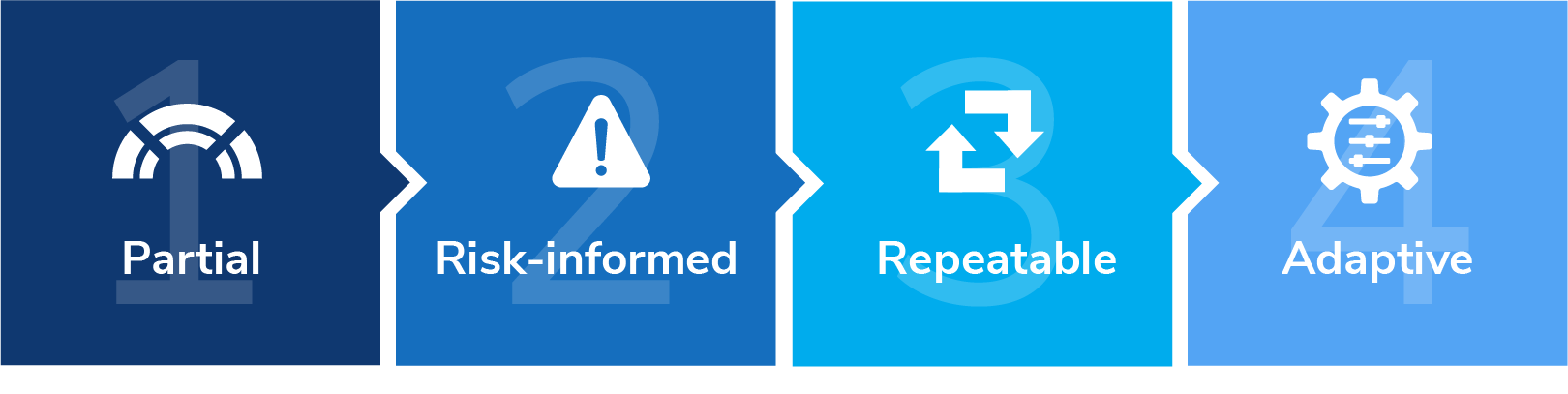
When implementing the NIST CSF, businesses may encounter confusion regarding the distinction between tiers and maturity levels. While tiers provide guidance on current cybersecurity practices and risk management coordination, maturity levels assess an organization’s progress in implementing these practices over time. Tiers help evaluate the adequacy of existing activities based on regulatory requirements and risk tolerance, while maturity levels track the evolution and effectiveness of cybersecurity efforts.
Organizations should regularly assess their readiness to tackle new and emerging threats, as well as old ones. Although the NIST Cybersecurity Framework should not be taken as a maturity model, using a self-assessment tool can help businesses keep track of their security program and identify the areas in need of improvement.
Companies can move up the four tiers by continuously improving their security maturity to the point their approach becomes proactive enough to counter more advanced threats.
Here are the four tiers, which we will discuss in-depth in Chapter Five:

Tier 1 Partial
At the lowest tier, cybersecurity risk management has not been formalized and documented. Instead, threats are countered on an ad-hoc basis, typically in a reactive manner.

Tier 2 Risk-informed
Often, there will be a few controls and policies in place to protect digital assets, but management tends to address risk as they appear.

Tier 3 Repeatable
At this level, organizations have established repeatable processes to counter threats, and a formal risk-management process and security policies have been defined. This is the minimum level that most organizations will want to achieve.

Tier 4 Adaptable
The final and highest tier centers around continuous improvement and adaptability. Companies that have reached this tier regularly conduct risk assessments and adapt security policies and procedures to counter the latest threats.
The tiers can provide an exceptional way to benchmark your existing security measures. And by obtaining an outside view, you may well uncover issues you didn’t know existed –– a critical safety measure during a time when external threats pose the most risk.
It’s easy to see how this assessment tool can offer benefits. However, other relevant advantages should be considered as well.
Benefits of NIST Cybersecurity Framework
Regardless of whether your company reaches Tier 4 right away, utilizing the NIST CSF is a strong step toward unifying business leadership and IT security. Without alignment between the needs of business leaders and the demands of cybersecurity, cybersecurity teams have traditionally found themselves operating in silos. Consequently, security leaders were often viewed as those who said no to innovation.
The NIST CSF can improve the relationship between business and cybersecurity and equip security leaders to become better communicators. To unify everyone this way, the CSF is heavily focused on risk management – a concept business leaders understand very well.
Unlike other cybersecurity frameworks that address only security measures, the NIST framework addresses the entire incident lifecycle, including what to do in the event of a successful attack. In short, it helps organizations prepare for practically any scenario.
Even smaller businesses can realize this benefit. Unlike large companies with fully staffed in-house IT security teams, smaller businesses can overcome these challenges by working with the right technical partners, such as security consultants and managed security services firms. MSPs can provide valuable services to support and provide counsel about very specific concerns, such as defending against ransomware or providing exceptional cloud security. To learn more about how a MSP can help your small business, click here.
Defending Against Ransomware
As cyber extortion becomes more common, NIST has responded by publishing a new draft on protecting against ransomware, which serves to complement the CSF. The addition to the framework features the ransomware profile, which can help organizations determine their state of readiness in effectively tackling the nightmare of cyber extortion.
Some businesses falsely assume that ransomware can easily be countered by antivirus software, but they have not taken into consideration the continuing rise of new variants. Additionally, these attacks are often carried out in conjunction with highly targeted social engineering scams, such as business email compromise (BEC) attacks. Many of these attacks can evade standard security controls, which is why the NIST Cybersecurity Framework recommended controls go beyond antivirus software.
While antivirus software should be used at all times and updated automatically, it should also be set to automatically scan email attachments and external media. That being said, most ransomware exploits vulnerabilities in outdated or unsupported operating systems.
Complicating matters further, the risks of ransomware attacks are even greater now that so many people are working from home and using their own devices for work. Because of this, organizations need to implement strict policies governing the use of third-party apps. In a perfect situation, no sensitive company data would be stored on employee-owned devices in the first place. Ideally, employee devices should only be access points to company apps and data hosted in the cloud. This approach allows administrators to restrict access by using standard user accounts without administrative privileges while also ensuring full visibility into their data.
Another crucial control area that the NIST Cybersecurity Framework deals with is security awareness training. Remote workers and everyone on your team should undergo regular awareness training so that they understand the risks and how they are spread.
Lastly, the latest ransomware profile also outlines concrete steps that organizations can take to recover from a ransomware attack. These steps focus on incident recovery planning, communications, and backup and restoration.
Though any organization can use these guidelines, ones that have already implemented the broader NIST Cybersecurity Framework can be most successful. Finding a dependable technology and security partner is essential for small businesses to achieve the same level of protection that big enterprises can accomplish.
Ensuring Safer Cloud Security
In this era of remote work and hyperconnectivity, cloud computing is essential for businesses. Yet cloud computing also carries its own set of security concerns. Simple logic tells us that the ability for your employees to access business-critical apps and data from anywhere and on any device means that bad actors also can do the same.
When the first version of the NIST CSF was released, cloud computing was relatively new and had yet to be widely used across all industries. Now that the era of cloud computing has arrived, the latest edition, along with the supporting documentation from NIST, provides guidance for external cloud infrastructure. While the framework does not cover all the important issues regarding cloud security, such as auditing and shared responsibility, it does lay out the critical foundations. Because most organizations still rely heavily on internal infrastructure, including networking hardware and endpoints, these systems need protecting just as they always did. Compliance with the framework helps secure both internal and external infrastructure, whereas many competing frameworks focus on only one or the other.
Just like the framework itself, cybersecurity should not live in isolation. Instead, it needs to be deeply integrated with your comprehensive strategy. Far from just being a necessary evil, it is now a critical part of a company’s value proposition. As Charles IT client, Michael Mullin, Chief Operating Officer of Environmental Systems Corporation, once stated, “We just weren’t able to do what we needed to do with what we had. “ He added, ”IT is probably the thing I’m most proud of now,” which showcases how beneficial it was for his organization once they made cybersecurity a core part of their business strategy. Let’s take a closer look at how the core functions serve to strengthen cybersecurity.

NIST Core Functions
To fully understand how the NIST CSF can benefit your company, it’s helpful to start by viewing the framework’s core functions.
As one of the world’s leading authorities on information security, NIST draws from numerous best practices, regulatory standards, and other frameworks. The Framework Core is broken down into six(6) functions, 22 categories, and 106 subcategories, as opposed to previous versions’ five(5) function areas, 23 categories, and 108 subcategories and dozens of resources, such as national and international standards and compliance regimes. The function areas are at the top of this hierarchy and are meant to highlight the role of each individual stage of the risk-management lifecycle.
Keep in mind that these core functions span the entire incident lifecycle, from identifying potential threats and assets to disaster response planning.
The NIST framework is highly versatile. It does not prescribe any specific products or services, which also means it is vendor-agnostic. As such, organizations can implement the framework in any way they want.
To become fully compliant with the framework, businesses need to achieve all desired outcomes across all six of the NIST CSF core functions. Let’s review these outcomes and explore what they entail with greater detail below:

1. Govern
This function aims to assist organizations in developing and supervising a cybersecurity strategy that aligns with their overarching mission and risk tolerance. It acknowledges cybersecurity as a crucial component of governance and strategic decision-making, guaranteeing that cybersecurity initiatives are not merely reactionary but proactive and aligned with the organization's goals. This core function addresses organizational context, risk management strategy, cybersecurity supply chain risk management, roles, responsibilities and authorities, policies, processes, and procedures, and oversight.
2. Identify
This function aids organizations in identifying cybersecurity risks that are tailored to their circumstances and connects these risks to the organization’s mission and risk appetite highlighted in the Govern section. This approach guarantees that cybersecurity measures are prioritized according to their potential impact on the organization's goals and objectives. This function addresses asset management, risk assessment, and improvement.

3. Protect
Protection of the digital assets identified in the previous core function is the goal of this step. The objective is to ensure all possible measures are in place to protect against threats either old or new and to ensure the continued delivery of business-critical services. The categories include Access Control, Awareness and Training, Data Security, Maintenance, and Proactive Technology. There is a major emphasis on the importance of proactive cybersecurity, rather than just relying on conventional reactive measures, such as antivirus scanners.

4. Detect
Inherently, protecting against threats demands the ability to detect them in the first place. Detection is paramount in the case of new and emerging threats that are not likely to be prevented by usual antivirus or firewall solutions. This function area has three categories: Anomalies and Events, Security Continuous Monitoring, and Detection Processes. Detection areas such as these are where technical solutions such as security incident and event management (SIEM) and managed detection and response (MDR) come into play.
5. Respond
This function area addresses incident response, with the goal of mitigating risks and preventing incidents that could result in serious damage. Remember, the NIST CSF rests on the fact that incidents will occur, no matter how robust your protective measures are. The five categories in this area are Response Planning, Communications, Analysis, Mitigation, and Improvements. This function focuses heavily on continuous improvement by leveraging the power of analytics to boost resilience to future incidents.
6. Recover
This function, a focus on recovery, is one that every organization must be prepared for, like it or not. It covers how to recover from a data breach or ransomware attack. The goal is to prevent the incident from worsening and to minimize lasting damage to the business. The three categories are Recovery Planning, Improvements, and Communications. Disaster recovery measures should be properly coordinated and based on the organization’s ability to tolerate a certain degree of risk.

NIST CSF Categories & Controls
Compliance with NIST SP 800 53 is mandatory for federal agencies and organizations making up the Defense Industrial Base. That being said, the NIST Cybersecurity Framework controls set the standards for security, and even though the controls were originally released with critical infrastructure in mind, they have since been widely adopted by multiple different industries. Across the six NIST cybersecurity framework phases there are 23 control categories. The categories are then divided into more specific control subcategories, of which there are 108.
These controls address everything from governing and identifying what needs to be protected to responding to and recovering from an incident. Unlike other cybersecurity frameworks that focus primarily on protective measures and detection capabilities, the NIST Cybersecurity Framework focuses on the entire lifecycle of incident management routines.
By taking a unified approach to the overall process, while still giving organizations control over how they implement the 23 control categories, this framework provides flexibility. Each control category has its own subcategories that provide actionable advice and resources to help organizations achieve the best outcomes and bolster their cybersecurity.
For example, the control category Identity Management and Asset Control under the Protect function area contains seven subcategories, along with their respective resources. Resources include references to other standards and frameworks, such as the NIST Special Publication 800-53.
When adapting the framework to the unique needs of your organization, the first thing to do is build out your cybersecurity profile. This profile will reveal the alignment between the requirements and objectives of your organization and its existing resources and appetite for risk. It will serve as the foundation for your requirements and controls.
Before prioritizing remediation based on severity, available budget, and business priorities, most organizations start with a cybersecurity gap assessment that looks for potential weak spots in their environment. Importantly, a NIST CSF gap assessment should encompass all relevant subcategories and consist of a profile of their current state and the target profile. Additionally, the target profile should include a prioritized implementation plan complete with a list of responsible parties and timeframes.
Key Points about the NIST Cybersecurity Framework
Here is an overview of what organizations need to understand about the key NIST CSF controls:

Building a complete inventory of your computing assets, including all networking components and data-bearing devices, is the first step toward implementation. Then, leaders should build out their risk profiles and prioritize their remediation strategies. The NIST Cybersecurity Framework mapping process can be difficult and time-consuming, considering the current complex hybrid and multi- cloud computing environments. Still, it is an essential step— you cannot expect to protect what you don’t know about.

The second and third function areas of the framework cover protective measures and detective measures, respectively. Protective measures include categories such as identity management and authentication and access control, awareness and training, and data security. Precisely how companies deal with these measures is a choice, but common methods include anti-malware, intrusion detection and prevention, and enterprise-grade firewalls.
The Detection function includes areas such as continuous monitoring, detection processes, and the management of anomalies and events. These functions can be outsourced in the form of managed detection and response (MDR) or security incident and event monitoring (SIEM) services.

The fourth and fifth function areas of the framework concern how organizations respond to an incident and how they recover from a disaster. Incident response plans primarily serve to stop attacks in progress and mitigate their effects. By contrast, recovery places an emphasis on what to do in a worst-case scenario, such as a data breach. Every organization, no matter the sophistication of its prevention and detection measures, should take the view that it is not a matter of if a disaster will happen, but when.

Lastly, the newly added Govern function addresses the need to establish a strong governance framework for managing cybersecurity risk organization-wide. While aspects like leadership commitment, risk management strategies, and resource allocation existed in the previous version of NIST CSF, they are now specifically highlighted within the Govern function. This emphasizes the important role of leadership in creating a cybersecurity culture within an organization.
In the dynamic and unpredictable world of information security, the only constant is change. No business can afford to rely on the same processes for years on end, which is why it is necessary to continually revisit the controls.
Mapping NIST CSF Controls
While the NIST CSF controls set the standards for information security, which controls you apply and how you apply them depend on your unique business environment.
Control mapping is the process of uniting two or more compliance domains or sets of business requirements to build a strategy that aligns to your distinct needs. Important factors to consider are your appetite for risk, the nature of your technology infrastructure, and your industry.
There are countless NIST Cybersecurity Framework examples out there. However, while it is always a good idea to see what other businesses similar to yours are doing, keep in mind that no two information security environments look exactly the same. Thus, NIST Cybersecurity Framework mapping is ultimately an individual effort.
As companies get ready for a security and compliance audit, the mapping controls can provide full visibility into the security environment. This visibility is extremely useful for organizations preparing to earn their Cybersecurity Maturity Model Certification 2.0 (CMMC 2.0), or working to achieve System and Organization Controls 2 (SOC 2) Compliance, for example.
In the end, control mapping gives organizations a cohesive and relevant way to ensure they meet the required business outcomes covered by the NIST Cybersecurity Framework. To get started with the process, you should obtain the help of an expert security and compliance consultant who will guide you through each stage and function area of the framework and offer advice and solutions tailored to the unique needs and characteristics of your business.
Some businesses find that starting with a checklist can help them plan for the conversation with an outside security consultant.
NIST CSF Control Checklist
As discussed, the NIST CSF controls span six function areas, 23 categories, and 108 subcategories to ensure comprehensive coverage. Use this checklist to help make sure you are prepared.
1. Identify

Asset management:
Create a complete inventory of all devices, accounts, personnel, data assets, facilities, and their risk profiles.
Business environment:
Define the organization’s mission, stakeholders, objectives, and activities to inform cybersecurity roles.
Governance:
Draft the policies and procedures intended to manage and monitor the organization’s regulatory, risk, and operational environments.
Risk assessment:
Assess, qualify, and quantify the risks facing your business to prioritize the next steps.
Risk management strategy:
Identify your priorities, constraints, and tolerance to risk to support operational decisions.
Supply chain risk management:
Apply the previous two categories to the context of supply chain risk management.2. Protect

Identity management, authentication, and access control:
Establish a robust way to grant and revoke access rights, ideally using multifactor authentication.
Awareness and training:
Implement a documented training program for personnel and partners to ensure everyone understands your policies and procedures.
Data security:
Ensure that data at rest or in transit is protected by encryption and that all devices are correctly tracked and managed.
Information protection processes and procedures:
Establish a way to enforce your policies and procedures and identify the scope and key roles and responsibilities.
Maintenance:
Create a maintenance program for managing and maintaining all data-bearing assets and system components.
Protective technology:
Establish protective measures, such as anti-malware, spam-filtering, and security incident and event management (SIEM).3. Detect

Anomalies and events:
Establish a way to detect anomalous activity and the potential impact of such events.
Security continuous monitoring:
All assets and networks must be monitored around the clock with a solution such as managed detection and response.
Detection processes:
Enforce a cybersecurity-aware company culture by ensuring that detection processes and procedures are properly maintained.4. Respond

Response planning:
Determine how and when incident response plans are executed and maintained.
Communications:
Identify the key roles and responsibilities of your incident response personnel, including any external support from law enforcement and other third parties.
Analysis:
Establish an effective way to analyze incidents to ensure an appropriate response and support future remediation plans.
Mitigation:
Perform activities to prevent the proliferation of an incident and mitigate its effects on your organization.
Improvements:
Response activities should draw upon your audit trails to determine exactly what went wrong and improve based on these insights.5. Recover

Recovery planning:
Document your disaster recovery processes and establish ways to minimize damage by restoring affected systems as quickly and as safely as possible.
Improvements:
Create a plan for identifying the strengths and weaknesses of your IT incident recovery methods to improve them in the future.
Communications:
Recovery activities must be properly coordinated, which means all personnel and third parties must be clearly aware of their roles and available to contact.6. Govern

Stakeholder and Legal Expectations Comprehension: Understand the demands of stakeholders and adhere to legal requirements regarding cybersecurity.

Cybersecurity Alignment with Organizational Goals: Ensure cybersecurity measures are in line with the objectives and targets of your organization.

Risk Management Strategy Implementation: Implement and oversee a cybersecurity risk management strategy, including enforcing standards for third parties and maintaining accountability and incident response protocols.
Additionally, the Framework Implementation Tiers provide context as to how the organization views its cybersecurity risk and how it manages it.

NIST Implementation Tiers
Sometimes referred to as NIST maturity tiers, the implementation tiers are not a legal mandate. They are also different from a cybersecurity maturity model such as the CMMC 2.0.
With this in mind, the NIST framework tiers are meant to help decision-makers take stock of how they currently view their information security efforts and how they align with the control categories of the framework core.
Each of these implementation tiers is, in turn, broken down into primary components: risk management processes, risk management programs, and external participation.
Here’s an overview of the four NIST framework tiers:
Tier #1
At the lowest level, the measures put in place are largely reactive, rather than proactive, and they provide only minimal defenses. There is also likely to represent a lack of documented processes and procedures for mitigating risk and managing incidents before they could lead to serious damage. An organization that views itself as being in this tier likely has minimal understanding of the risks to its supply chains and other external stakeholders.
Tier #2
At this level, business leaders are aware of the major risks that face them, such as malware, state-sponsored attackers, and other malicious actors. They probably have procedures in place for protecting against and mitigating these threats. However, while they may have a reasonable degree of threat awareness, these tier-two organizations lack a unified strategy with consistent policies between departments. Similarly, they may also be aware of the risks to their supply chains, but lack the capacity to act on those risks with strong governance policies.
Tier #3
This is the minimum NIST implementation tier that most organizations will want to achieve. The hallmark of a robust information security strategy is repeatability. It should be possible to apply information security measures, procedures, and policies across the board and maintain full visibility into your data environment. Tier-three organizations have achieved this, and their practices are regularly updated to counter new risks and threats. They are also able to respond quickly to incidents and manage risk across their supply chains effectively.
Tier #4
These organizations have achieved a high level of security maturity and are able to counter the latest and most sophisticated threats. Unsurprisingly, the highest tier is also the most time-consuming and costly to implement, but it is vital in highly regulated sectors such as finance, healthcare, and critical infrastructure. Adaptive information security incorporates high- tech solutions, including machine learning-powered detection and response capabilities and security incident and event management (SIEM) and adaptive policies and procedures.
Assessing Your NIST Framework Tier Level
Aiming for the third tier is a realistic goal for most companies, and, as noted, it is essential in the instance of highly regulated industries such as critical infrastructure and finance. The fourth tier corresponds to the best information security strategy possible. Fortunately, however, it is possible for small businesses to achieve top-tier cybersecurity performance by partnering with an organization that offers key services such as managed detection and response (MDR) and security incident and event management (SIEM).
To assess your Tier level and determine your goal, you’ll want to consider the following:
-
Your appetite for risk
- Before assessing your NIST framework tier level, you should first determine where you want to be, and which risks you are willing to take. It is important to find a good compromise between innovation and risk management. -
Your governance capabilities
- Decide what you can measure. You can protect only what is on your radar, which is why the first step in assessing your compliance with the NIST framework is establishing your governance capabilities. Do you know precisely where your data lives and which controls are in place to protect your data? Do you have a clear picture of the risks facing your business? Do you have a documented program for mitigating the risks? To fully comply with the framework, your risk-management strategy needs to be centralized and applied across the organization. -
Your protective measures
- Determining your current NIST framework tier level shouldn’t be overly complicated. Protective measures should go far beyond conventional solutions such as anti-malware and firewalls. The ultimate goal should be to prevent threats from getting anywhere near your network in the first place. (As noted, solutions such as MDR and SIEM can help with this, since they provide proactive defenses that can be applied to your entire computing infrastructure.) -
Your response and recovery plans
- People need to be familiar with their roles and responsibilities when it comes to detecting a potential threat, such as a malicious email. If people don’t know how to react if, for example, they receive a phishing email, then your response strategy is likely in the lowest tier. The same applies to disaster recovery.
A NIST Cybersecurity Framework maturity assessment serves as the basis for your strategy. Most importantly, it should be capable of enabling an organization-wide conversation around information security risk.
Now that cybersecurity is top of mind for many potential customers, especially in the case of B2B transactions, compliance with the NIST framework adds value to your business.
NIST Implementation
Steps to Prepare
NIST implementation requires some forethought but can yield significant dividends. To help you plan, we’ve identified three crucial steps:
1. Establish your Goals
Set realistic goals that align with your specific data environment and risk level. Setting goals will allow you to measure success, while making it more likely you’ll earn the support of senior management. It is, therefore, important to establish goals that will be acceptable to both management and the IT department. Setting a clear budget is also an essential step as you’re setting your goals.
2. Create your Target Profile
You should build two profiles: one detailing your current situation, and another detailing where you want to be. These profiles should align with the NIST Cybersecurity Framework implementation tiers. To create your current profile, you should first conduct a security gap analysis, preferably with the help of an external partner, to determine where your current vulnerabilities lie. Armed with this knowledge, you will be able to refine your goals and create a target profile that meets your budgetary and operational requirements.
3. Build an Action Plan
A gap analysis will help you quantify and qualify your existing information security controls and procedures so that you can compare them alongside your target scores. The next stage of the process is turning these insights into a series of actions that you can take to improve your IT security posture. Your action plan must be aligned with the broader needs of your organization.
Remember, NIST CSF compliance isn’t something you do just once. Even after you’ve implemented your action plan, it will need to be updated regularly. Continued review helps to ensure your organization is always up to speed with latest threats and the security standards that are being introduced to counter them.
How an MSP Can Help with NIST Compliance
Even smaller organizations can achieve the same degree of security and compliance as large enterprises, particularly when managed services providers (MSPs) can help. With cyberattacks estimated to cost the U.S. $1.82 trillion by 2028, it’s never been more important to adopt a proactive approach to information security.
Here are the top ways that partnering with an MSP can help you implement your cybersecurity compliance framework:
Assess your Current Security Maturity
First determine where you currently are in your journey. This will help you build your
current profile which, in turn, helps you prioritize your remediation strategies to address
any vulnerabilities in your existing infrastructure. External vulnerability scanning with an MSP presents an obvious starting point, since it will evaluate your network from the outside looking in. This can also be done in conjunction with the NIST security assessment to evaluate how closely your strategy currently aligns with the framework.
Provide Security Awareness Training
The NIST Cybersecurity Framework aims to create a common language concerning information security and how it ties into broader business risk management. The framework addresses security awareness and accountability as much as it does technical controls and concepts. Thus, it is intended to be adopted organization-wide in a cohesive and comprehensive manner. An MSP that provides security awareness training can help toward your goal.
Monitor Security Events in Real-Time
Detecting potential security incidents as they happen is one of the primary function areas of the framework. Protective measures are another. Your network needs round-the-clock monitoring every day of the year. Chances are, however, that having a fully staffed 24/7 security team is impractical, especially for small businesses. A managed security information and event management (SIEM) solution can bridge that divide.
Implement Better Access Management
Most business workloads are handled in remote data centers in this era of cloud computing. They require a rethink in security. The traditional concept of a secure perimeter no longer applies in these distributed computing environments, hence why the emphasis should be on account-based security. Partnering with the right MSP can help protect online accounts with measures such as multifactored authentication.
Protect all your Data-Bearing Assets
The need to secure endpoints is greater than ever. Endpoints are any devices used by employees to access the resources they need to perform their roles, including employee- owned laptops and smartphones. Should any such device be reported lost or stolen, it could put your business at a serious risk of a data breach. Choosing the right MSP can help you meet endpoint protection compliance goals with measures such as endpoint encryption.
Implementing the NIST Cybersecurity Framework should be approached as a journey rather than a destination. Cybersecurity is a constantly evolving field, which is why it makes sense to have the right technical partners to regularly review and guide you through your security maturity.
The reality is that the NIST Cybersecurity Framework is extremely broad and exhaustive in its
approach. Attempting to achieve full compliance with the framework can be a huge task for a
typical small business, which isn’t likely to have a fully staffed IT security team. For this reason,
the best approach is to find the right partner who can guide you through the process and help
you implement the most suitable security processes and controls.
Every organization should start with a gap assessment to evaluate their existing cybersecurity posture and identify areas in need of improvement. Common unified solutions include outsourcing security management, implementing comprehensive security measures, and providing regular security awareness training.
Let Charles IT show you how we can work together on the NIST CSF to achieve your IT security goals. Talk to an expert today.