CMMC Cybersecurity Maturity Model Certification Explained

Learn about the CMMC cybersecurity framework and how CMMC 2.0 will differ. We’ll also help you get started on how to achieve CMMC 2.0 compliance.
What is MDR and Why Do You Need It?

Discover the importance of Managed Detection and Response (MDR) in cybersecurity. Learn how MDR helps organizations detect and respond to threats quickly, and why it’s a cost-effective solution for businesses of all sizes.
Do You Need GCC High to Be CMMC 2.0 DoD Compliant?
Learn about Microsoft GCC and find out if it’s a requirement for CMMC DoD compliance.
A Guide to CMMC 2.0 & DFARS Compliance Requirements
Everything contractors and subcontractors need to know about CMMC and DFARS compliance requirements.
A Quick Guide to the 3 CMMC 2.0 Levels

Learn more about the five Cybersecurity Maturity Model Certification (CMMC) levels and what you need to do to achieve the certification level you aim for.
Four Steps to Becoming CMMC 2.0 Certified
Follow these four steps to become CMMC certified and obtain contracts.
What is the Cybersecurity Maturity Model Certification (CMMC)

An introductory guide on what the Cybersecurity Maturity Model Certification is and how to pass a CMMC audit.
CMMC vs FedRAMP: Steps to Achieving FedRAMP Compliance
Learn the steps to achieving Federal Risk and Authorization Management Program (FedRAMP) compliance
Endpoint Encryption: The Foundation of a Secure IT Environment

Endpoint encryption is a crucial security measure for businesses to protect sensitive data from unauthorized access. Learn about its benefits, challenges, and tips for implementation for your organization.
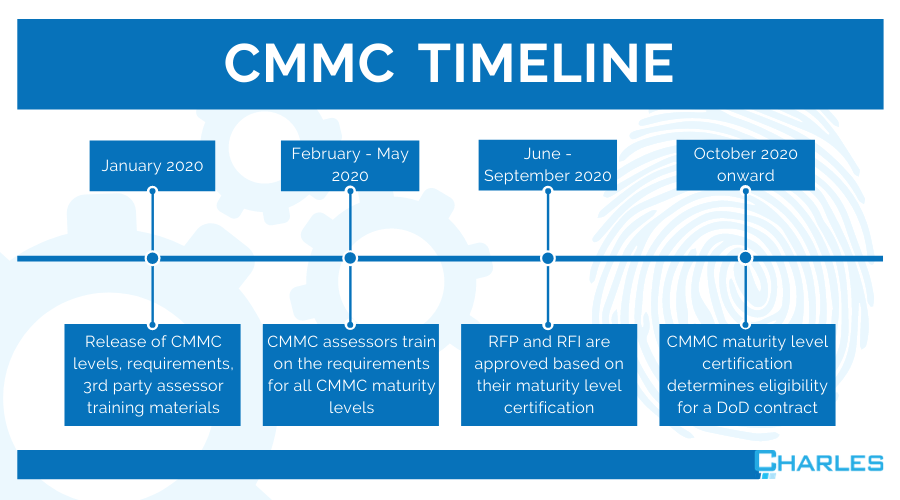
The Timeline for CMMC 2.0 Rollout: What You Should Know
Understand the rollout timeline, processes, and milestones of CMMC 2.0 so your organization can be best prepared when it finally becomes law.

